Application security that speaks human.
A senior application security engineer reviews your software, ranks what could actually hurt you, and writes it up in plain English.
AI is taking our jobs? Cool, when?
Copilot wrote 10k lines of code today. Nobody reviewed it.
AI catches plenty. Good. But it doesn't know your checkout trusts whatever price comes back from the browser. It doesn't know that tweaking a number in a link shows someone else's account. It doesn't know your admin pages are reachable from anywhere on the internet.
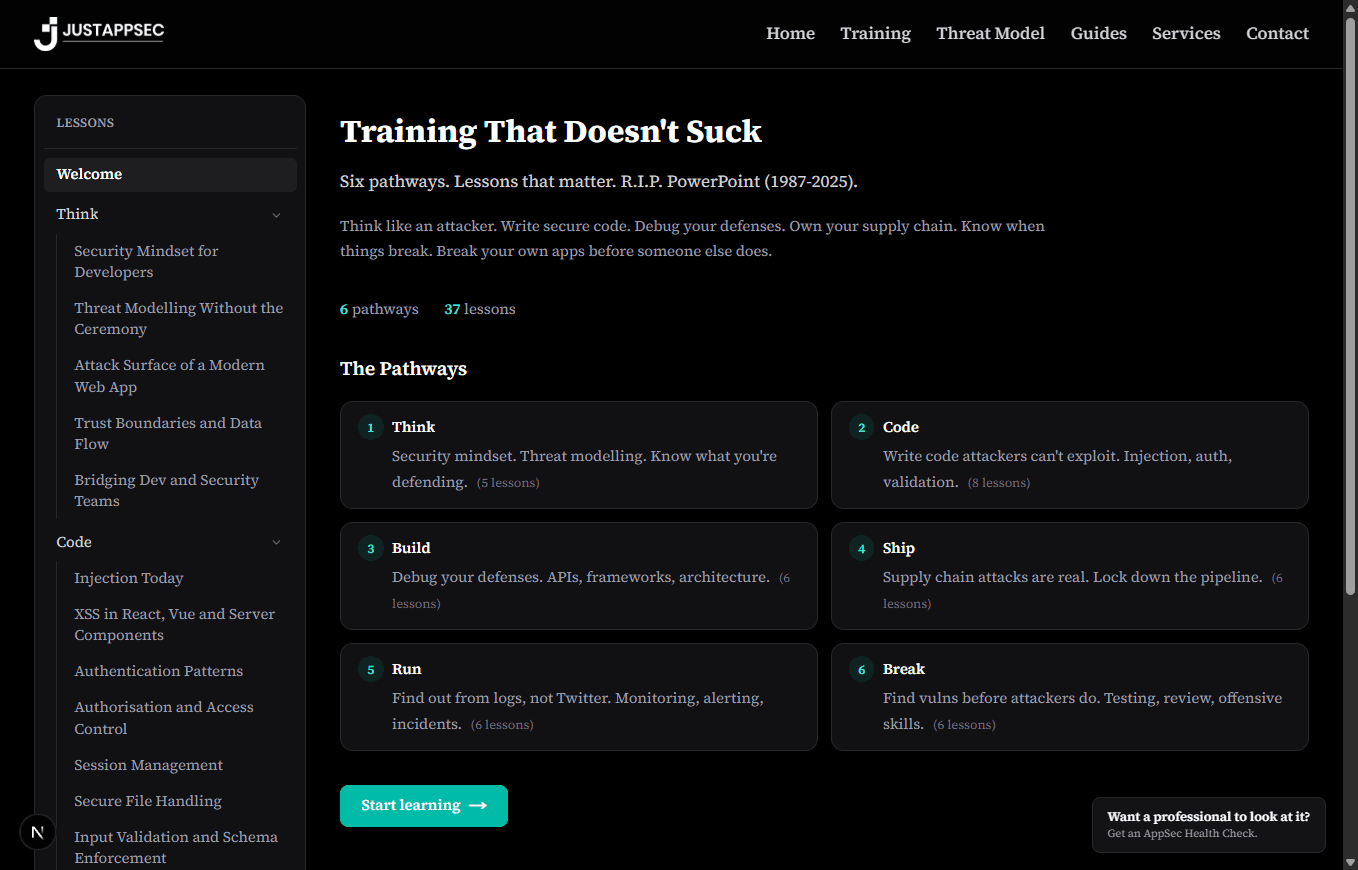
Security training that doesn't suck
Learn what you need to know, in the order it really happens.
Latest from the guides
Browse all guidesAutomated threat model updates with GitHub Actions
Use AI coding agents in CI to keep your threat model current. When code changes, the pipeline reviews the diff, updates the .justappsec file, and commits the result.
Read the guideDORA secure SDLC for development teams: a practical guide
DORA puts ICT operational resilience on a legal footing for EU finance. This guide translates its secure-SDLC and third-party requirements into developer-level controls.
Read the guideNIS2 for development teams: a practical bridge from EU directive to your codebase
NIS2 sets EU-wide security obligations for essential and important entities. This guide translates them into concrete controls for software teams shipping to those organisations.
Read the guide